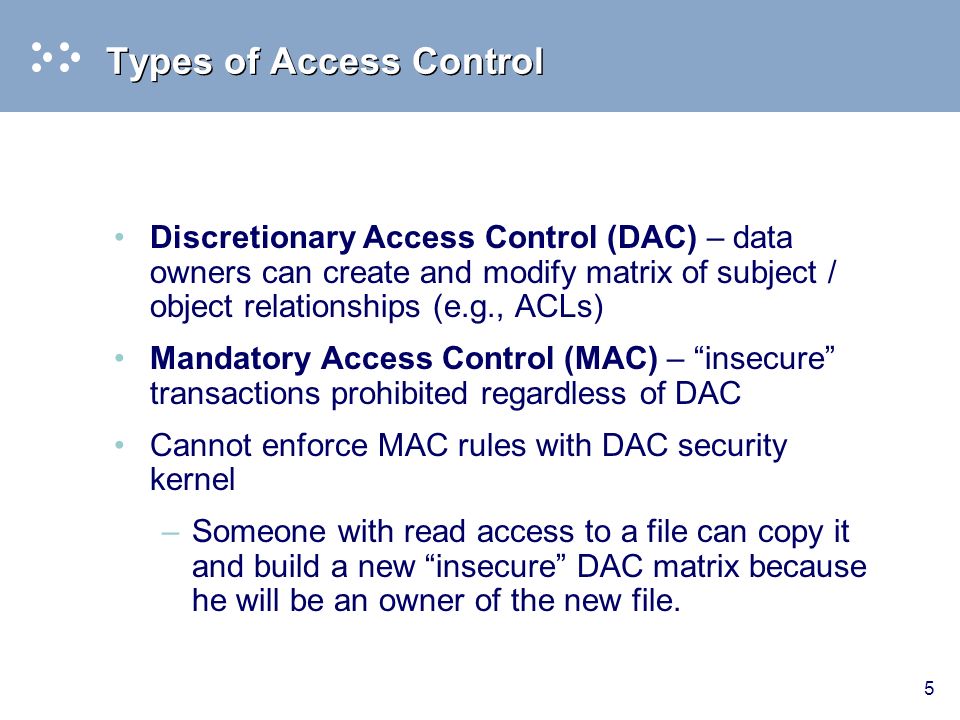
Generic metamodels for expressing configurations of (a) DAC; (b) BLP... | Download Scientific Diagram

Discretionary and Non-Discretionary Access Control Policies by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu
Session 2 - Security Models and Architecture. 2 Overview Basic concepts The Models –Bell-LaPadula (BLP) –Biba –Clark-Wilson –Chinese Wall Systems Evaluation. - ppt download

CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu
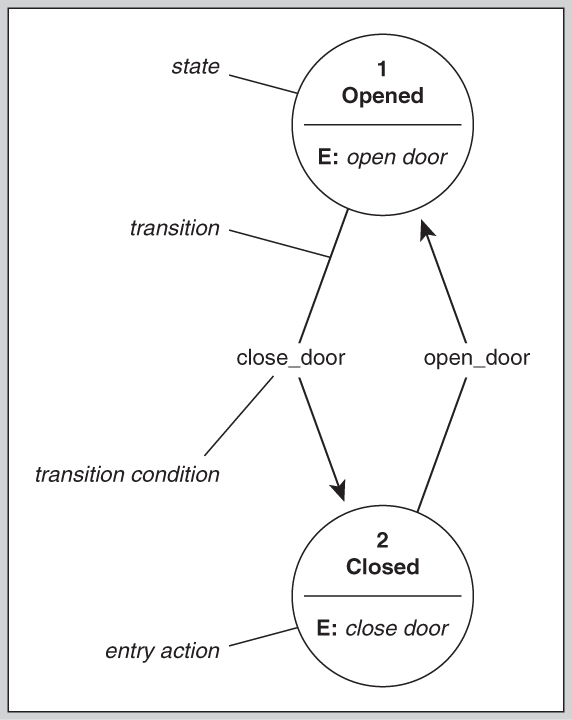
![PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/83fcec720b425bbc4e764ff167afaea6721dbb3e/4-Figure2-1.png)
PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar
![PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/83fcec720b425bbc4e764ff167afaea6721dbb3e/2-Figure1-1.png)
PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar
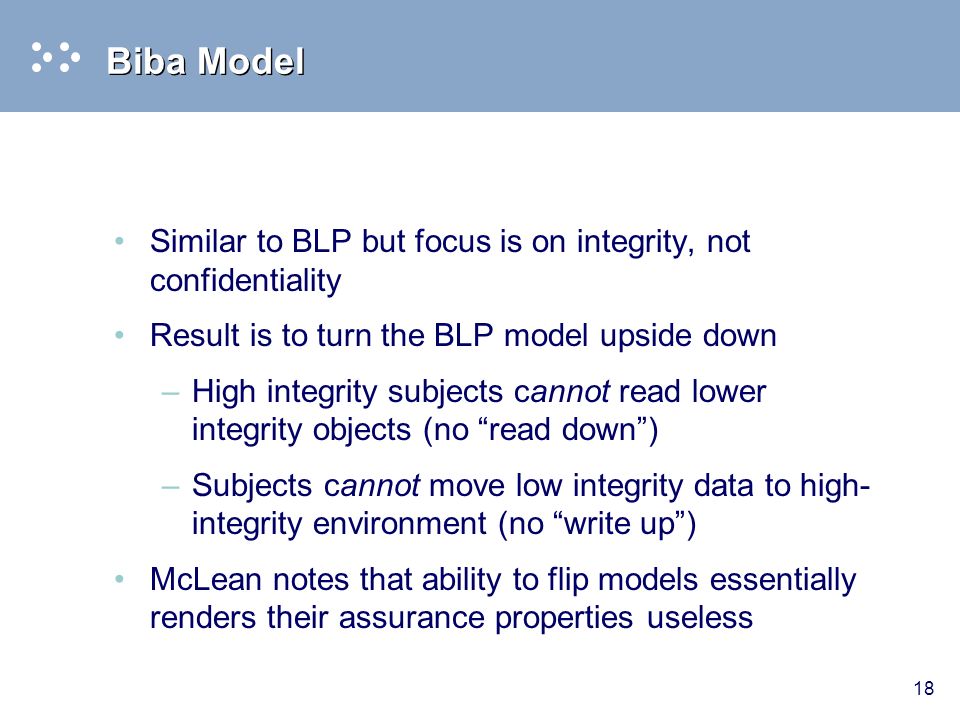
Session 2 - Security Models and Architecture. 2 Overview Basic concepts The Models –Bell-LaPadula (BLP) –Biba –Clark-Wilson –Chinese Wall Systems Evaluation. - ppt download